GitHub Deployment
Deploy and run the code of your WordPress site on the Bitpoke App using GitHub.
Time required: 15 minutes
To start, we’ll consider that you have already created a site on Bitpoke App and we will explain step by step how to store and deploy your site code on Bitpoke App from a GitHub repo(public or private).
You’ll need a GitHub account and also the content of your site’s wp-content/themes and wp-content/plugins and also any additional custom code. The site to be installed will be using a repository called mywpsite with a custom layout.
1. Create a repo on GitHub
You’ll need to store your code on your own GitHub repo that you should boot-strap with the Bitpoke Stack
example repo
as a starting point. To do so, you would need to visit this repo and click the green Use this template button and select the Create a new repository option. Fill in the repository name, we’ll use mywpsite and finalize by submitting the Create repository button. Make sure to select the right privacy for the project.
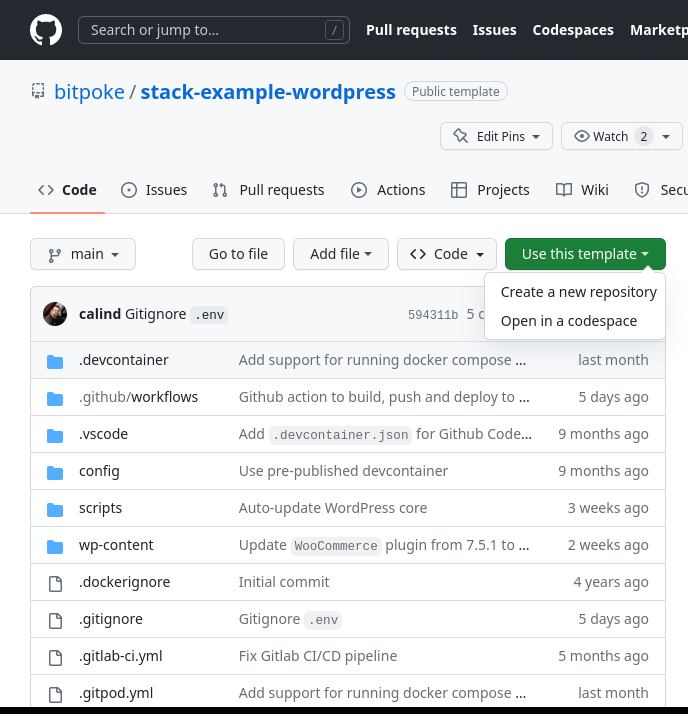
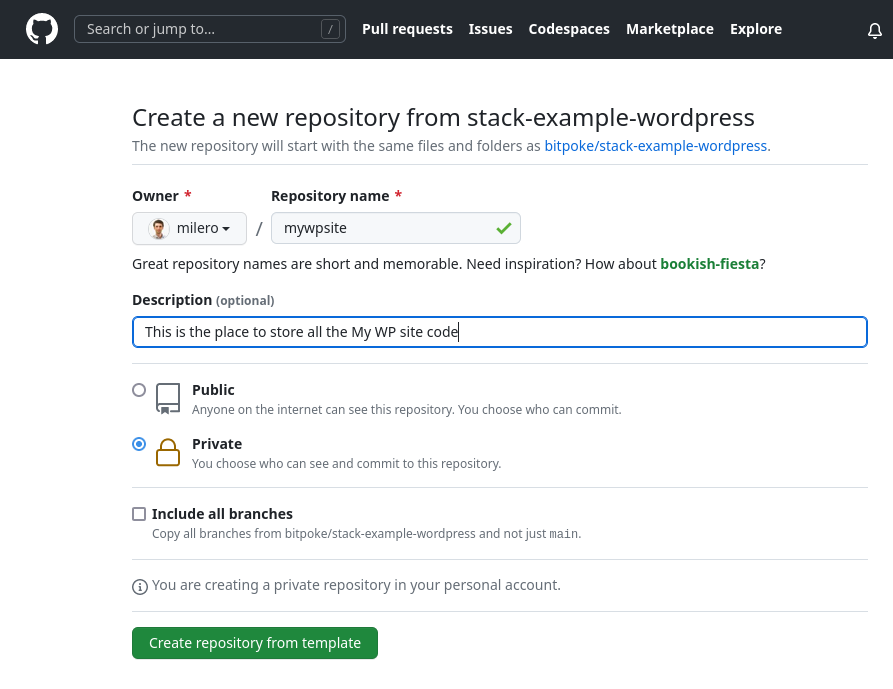
All done, so now you have set up the home for your site code. Feel free to add the code under the right location - plugins and themes.
2. Configure the CI/CD for the project
Next we need to configure the continuous integration and deployment for the site. This is possible via the Settings menu, section Secrets and variables -> Actions.
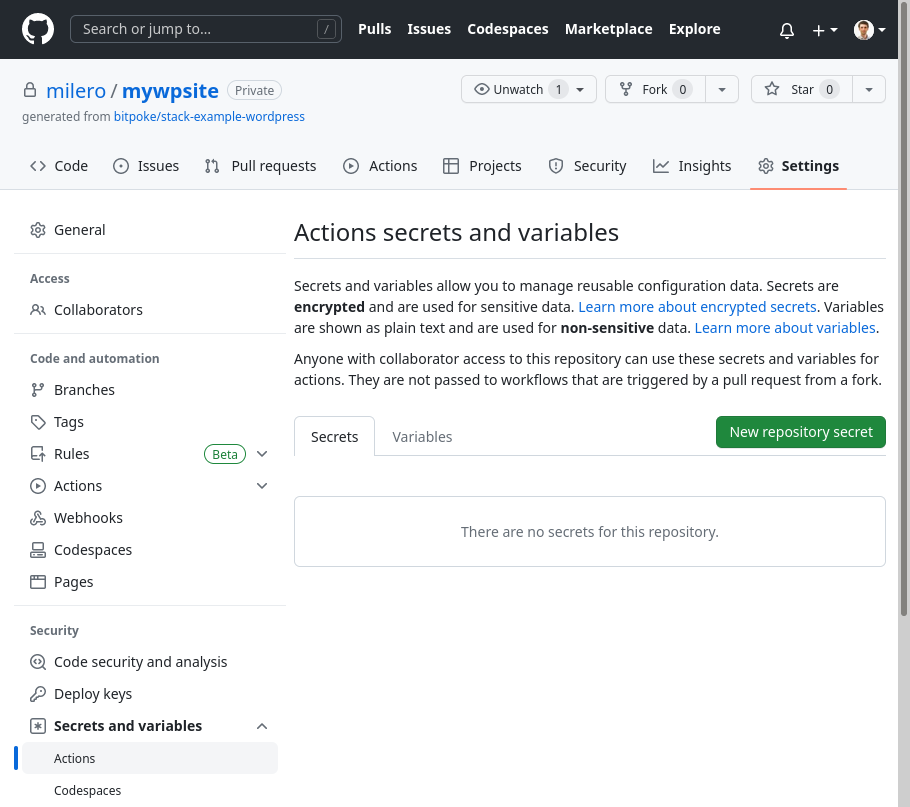
Open the Variables tab so that now you should see the green New repository variable button so you can click it to add the required variables to connect to your Google Cloud setup.
The variables that need to be entered are:
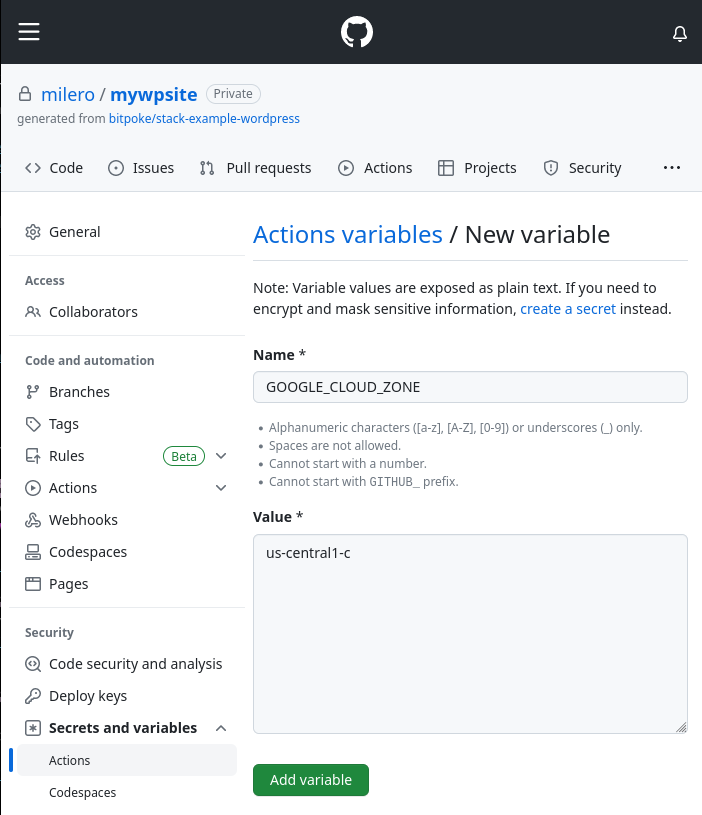
GOOGLE_CLOUD_ZONE
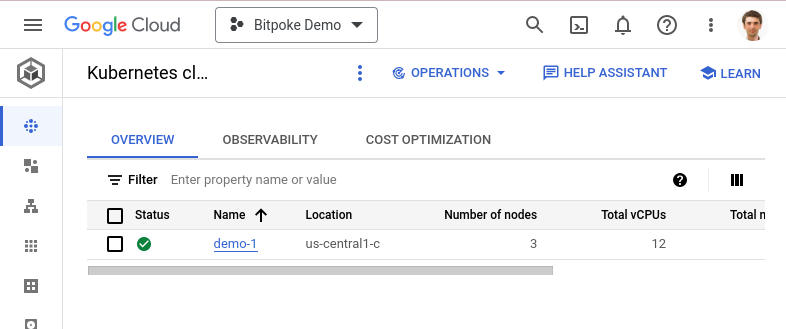
If you forgot the GCP zone your Kubernetes cluster is living, you can find it in the cluster overview page in Google Cloud Console
here
. The value in our sample is us-central1-c, you’ll find yours under the Location column.
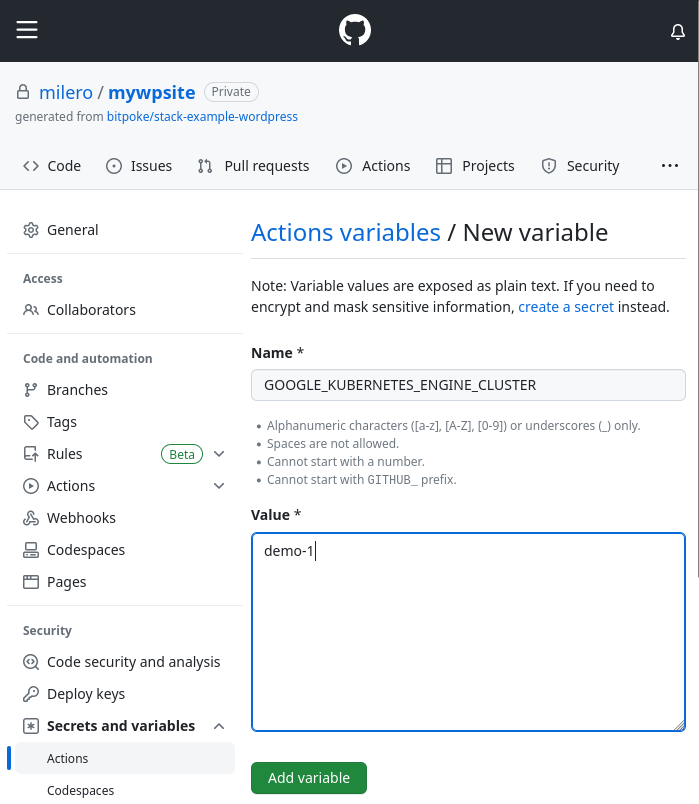
GOOGLE_KUBERNETES_ENGINE_CLUSTER
The value of this variable can be extracted from the cluster listing page under the column Name. In our case, it’s demo-1.
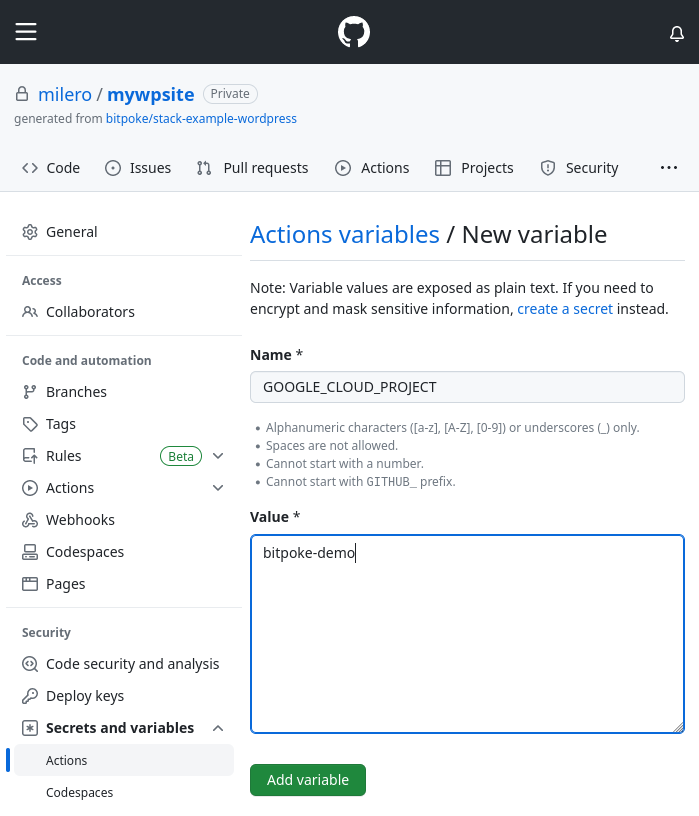
GOOGLE_CLOUD_PROJECT
You can find this value in the Google Cloud Console, in the Cloud overview -> Dashboard, accessible from the top left main menu.
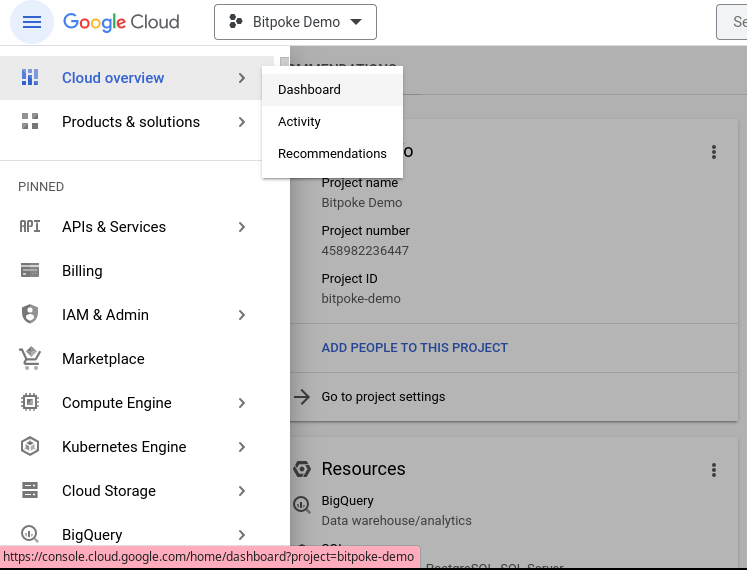
The value of the Project ID is bitpoke-demo and you can find it in the Project Info card, entry Project ID.
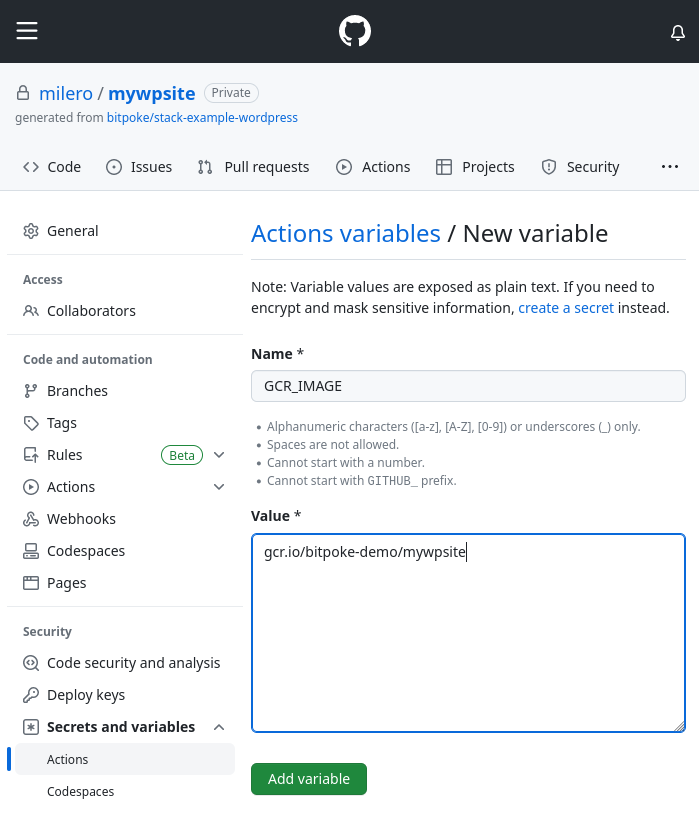
GCR_IMAGE
The value can be set to gcr.io/bitpoke-demo/mywpsite, using the GCP project value identified above.
BITPOKE_PROJECT:
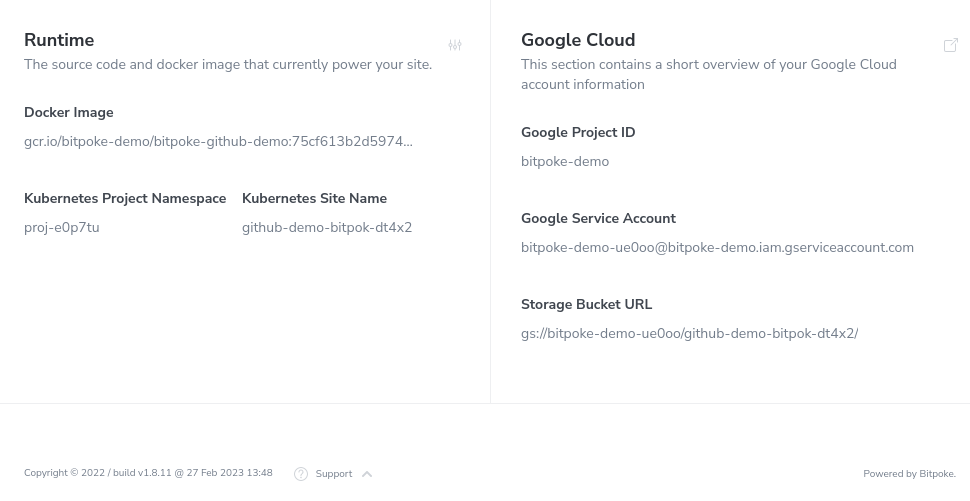
This value is easy to spot directly in the Bitpoke App, in the selected site Routing menu. It is listed under the Kubernetes Project Namespace. In our case it’s proj-e0p7tu.
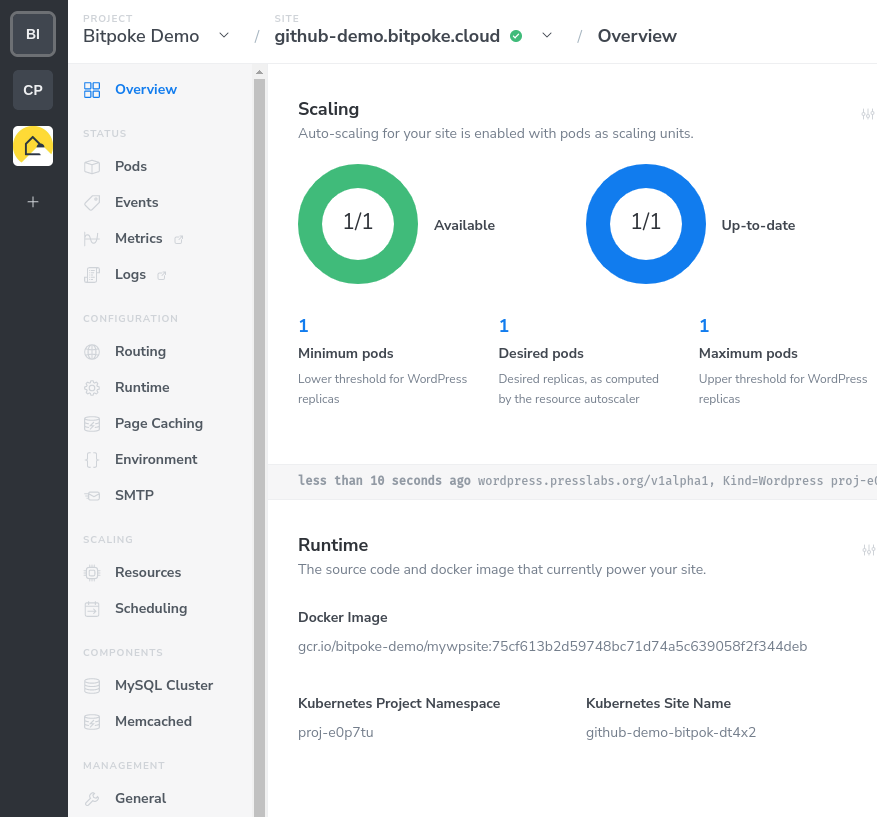
BITPOKE_SITE_NAME
The value for the Bitpoke Site Name can be found in the same Runtime screen of the Bitpoke App, under the Kubernetes Site Name label. It’s github-demo-bitpok-dt4x2 for our sample site.
3. Set up application key
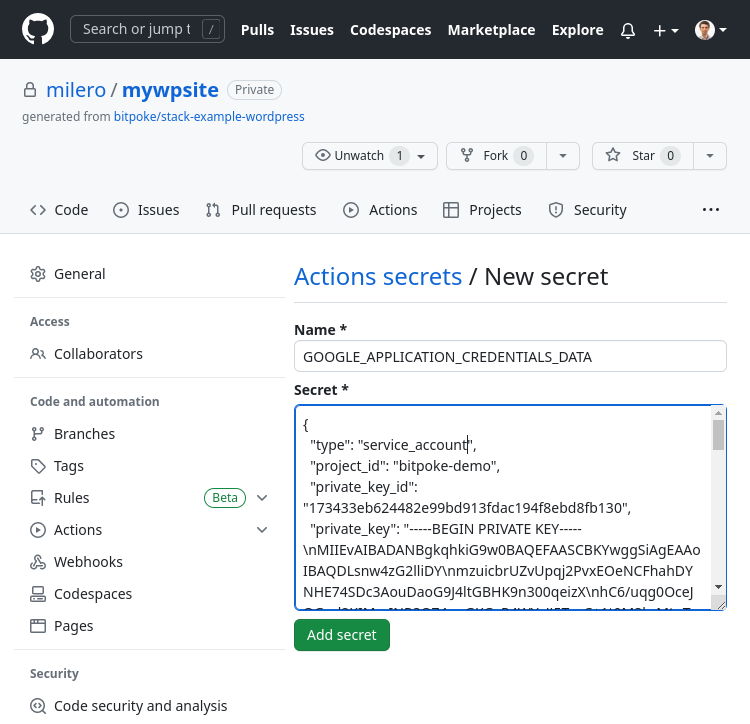
We will need to add a secret that will contain the JSON access key. The name of the secret will be GOOGLE_APPLICATION_CREDENTIALS_DATA. This will take a few easy steps, detailed below.
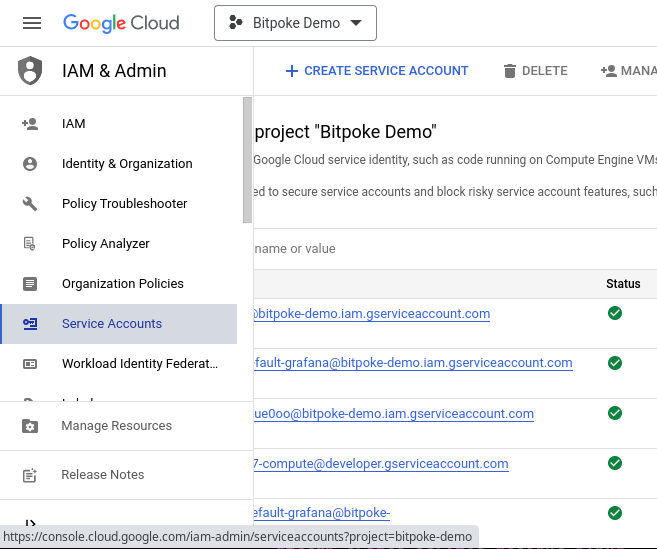
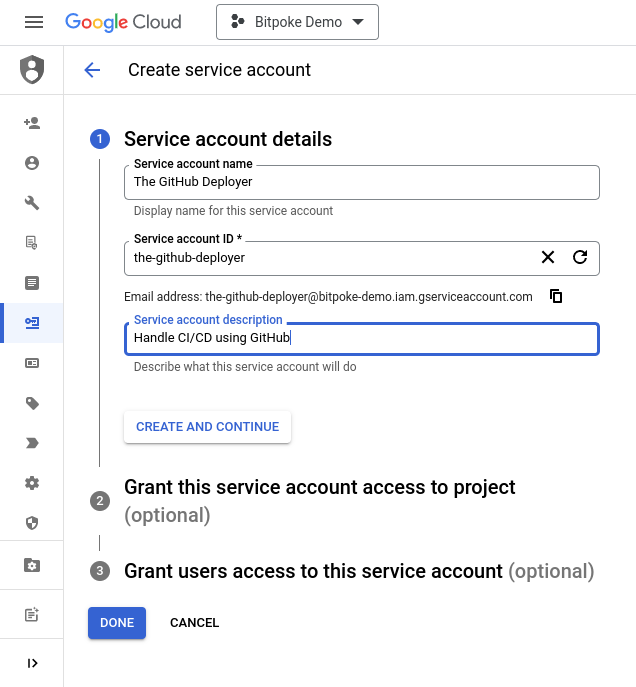
The first step is to create a service account in the Google Cloud Console, in the IAM Admin -> Service Accounts menu. Click the Create service account button.
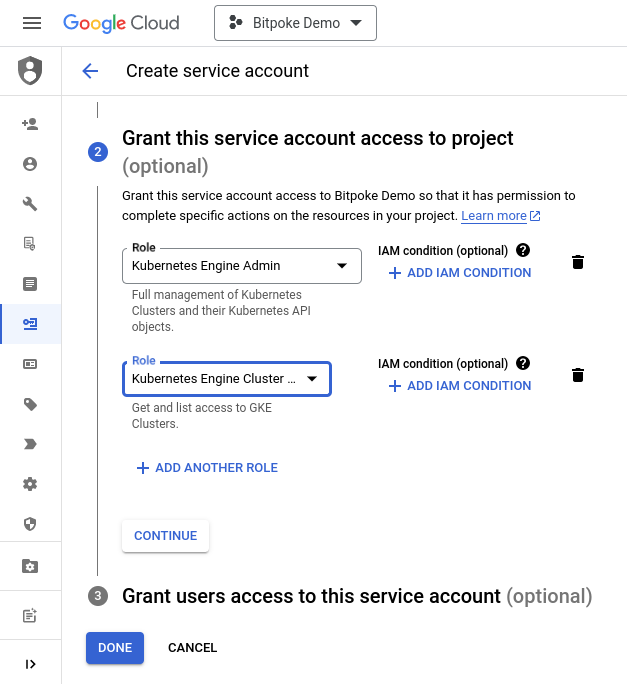
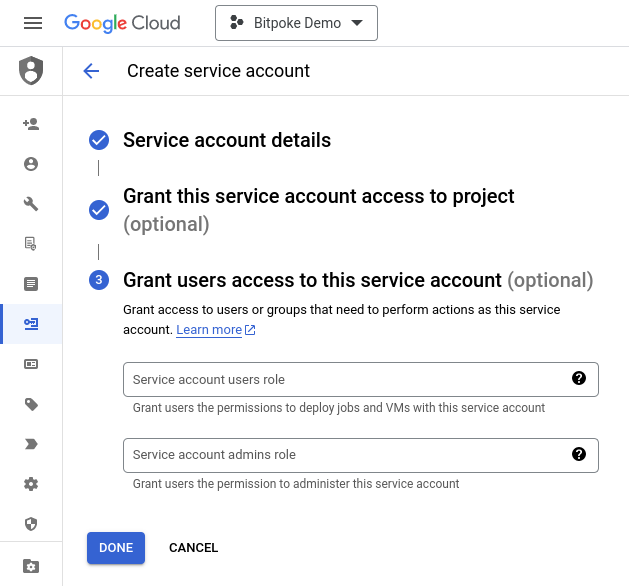
Fill in a relevant name, such as The GitHub deployer. Then press Continue. Grant Kubernetes Engine Admin, click Add another role and then Kubernetes Engine Cluster Viewer. Click Continue and then click on the Done button finally.
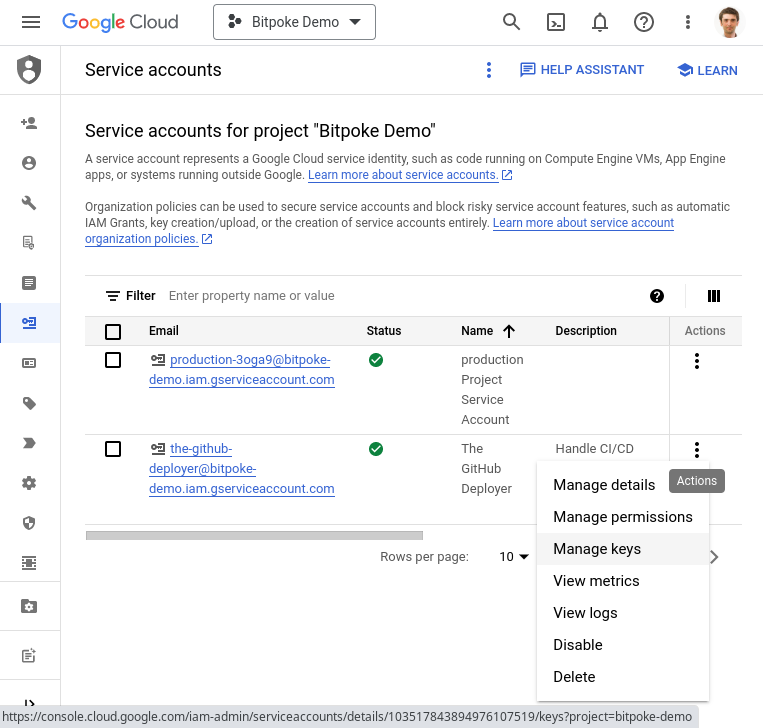
Second step is to generate the access key. You need to click on the triple vertical dots of the service account Actions column and then click Manage keys.
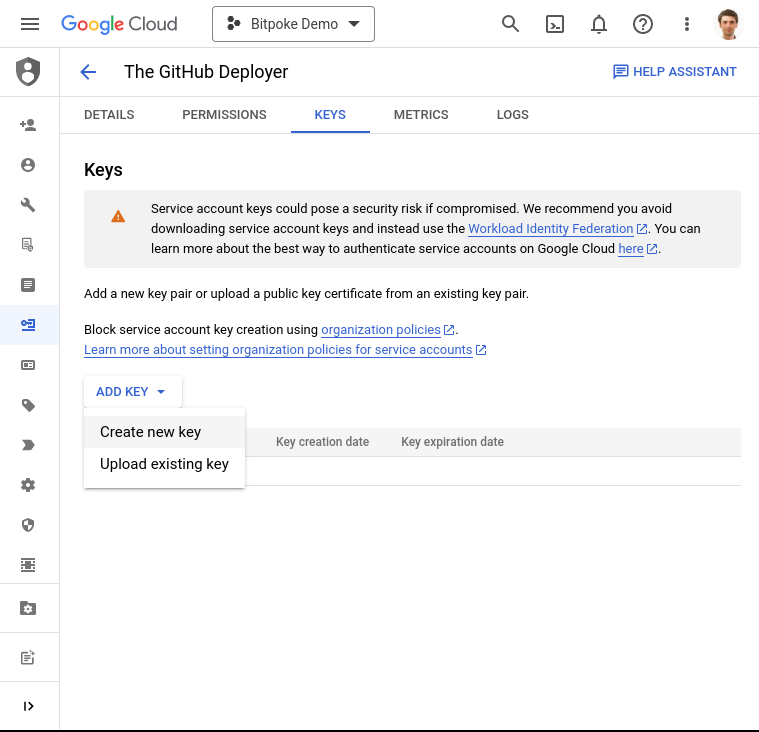
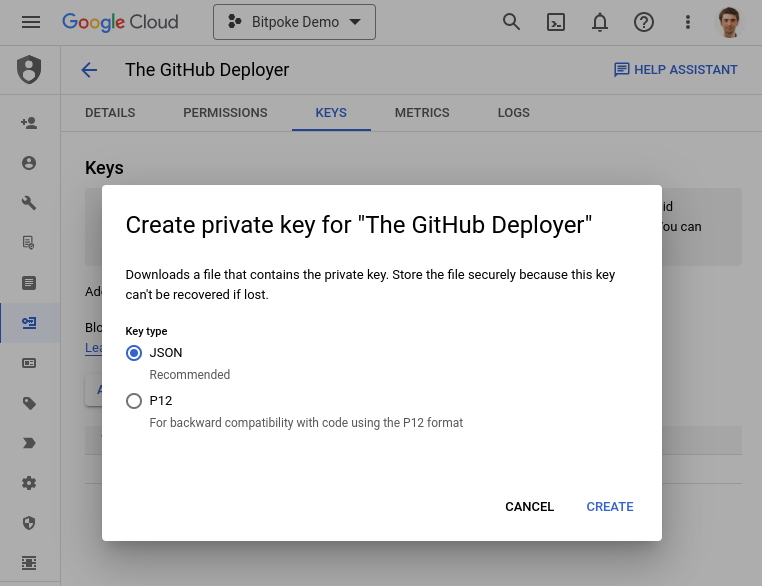
Click the Add Key button and select Create new key. Select JSON as Key type and press Create. You will be able to download the private key to your computer.
Open the key content with your text editor and copy the content of the key. Now it’s the moment to create in GitHub the secret named GOOGLE_APPLICATION_CREDENTIALS_DATA. Make sure to paste the key in the Secret text input. Click Add secret and you are done.
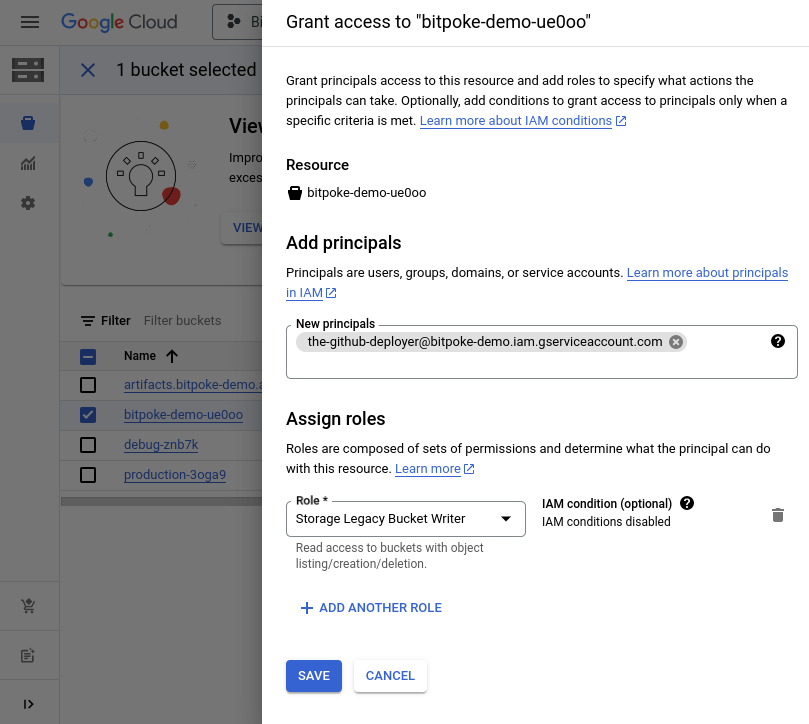
4. Grant bucket write permissions
The last step is to grant write permissions so that the generated Docker image can be written and stored on your Google Cloud account. For this, you’ll need to assign write rights to the GitHub deployer - the service account that you have just created in the first step.
Find out the ID of the storage bucket of your site in the Bitpoke App overview page. In our case, it’s bitpoke-demo-ue0oo, as the highlighted part between the protocol “gs://” and site name “github-demo-bitpok-dt4x02”.
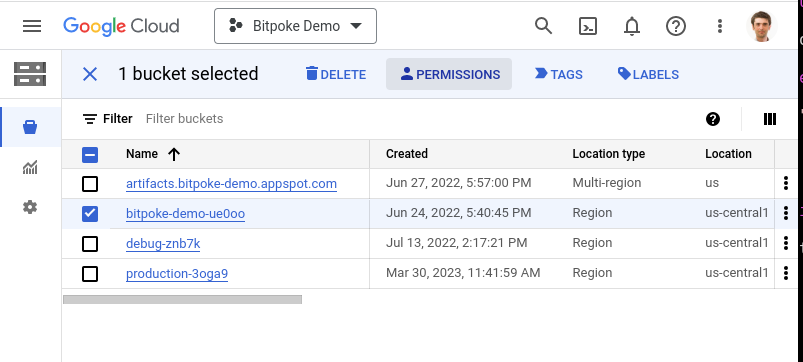
You’ll have to visit the Cloud Storage->Buckets menu. Select the appropriate storage bucket from the list and then click on the Permissions button.
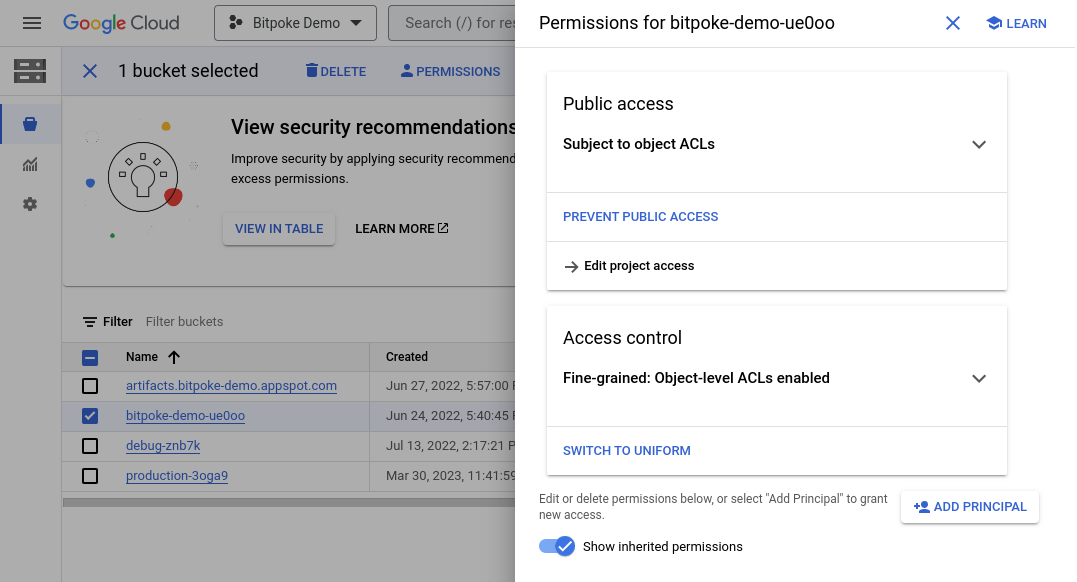
Click the Add principal button and add in the New principals input the service account - in our case it’s the-github-deployer@bitpoke-demo.iam.gserviceaccount.com and in Role select Storage Legacy Bucket Writer. Click Save and you are all good to use your new automatic GitHub deployment pipeline!